
In an era increasingly defined by digital reliance, the security of public institutions’ online infrastructure is paramount. Dallas homeowners and real estate professionals experienced this firsthand when the Dallas Central Appraisal District (DCAD) website, a crucial hub for property information, fell victim to a sophisticated ransomware attack in November. The incident sent ripples of concern throughout the community, with initial details about how such a significant cybersecurity breach occurred remaining scarce. This lack of immediate transparency left many in the dark about the integrity of vital public data.
The timing of this cyberattack could not have been worse. It unfolded precisely when residents were actively engaged in the process of paying their annual property tax bills. The DCAD website is an indispensable resource, providing detailed appraisal information essential for accurately determining tax liabilities. Its sudden unavailability, coupled with the uncertainty surrounding the breach, created significant anxiety and logistical challenges for thousands of taxpayers and real estate stakeholders across Dallas County. The disruption underscored the critical role that digital public services play in the daily lives of citizens and the severe consequences when these services are compromised.
Following the breach, federal authorities were promptly engaged, with the FBI initiating an investigation into the attack. Reports quickly emerged, pointing fingers at Royal Ransomware, widely recognized as one of the world’s most prolific and aggressive online extortion groups. This identification highlighted the serious nature of the threat and the sophisticated tactics employed by cybercriminals targeting critical infrastructure. The involvement of such a high-profile group amplified concerns about the security vulnerabilities inherent in public sector digital platforms and the broader implications for data protection.
Ultimately, a resolution was reached, albeit at a cost. According to an investigative report by the Dallas Morning NewsWatchdog, DCAD paid a sum of $170,000 to the hackers. This payment, drawn from the district’s reserve fund, represented a fraction of its substantial $34 million operating budget. While significantly lower than the cyberterrorists’ initial demand, the decision to pay a ransom is always contentious, raising questions about encouraging future attacks and the ethical dilemmas involved in negotiating with criminal enterprises. The swift, yet costly, resolution aimed to restore essential services, but the episode left a lingering shadow over DCAD’s cybersecurity posture.
Despite repeated attempts by daltxrealestate.com to obtain official statements or insights, DCAD Director of Community Relations Cheryl Jordan and longtime Chief Appraiser Ken Nolan remained unresponsive to requests for comment. This silence from key officials only added to the public’s frustration and the sense of unease surrounding the incident. Transparency and open communication are vital in building and maintaining public trust, especially when sensitive taxpayer data is at stake. The lack of dialogue fueled speculation and underscored the perceived gap in communication between public entities and the communities they serve.
After a period of significant downtime, the DCAD website, which meticulously manages an astounding 840,000 property accounts, was eventually reactivated in mid-January. While its restoration was a welcome relief for many, the incident served as a stark reminder of the fragility of digital infrastructure and the profound impact of cybersecurity failures on essential public services. The path to full recovery and rebuilding trust, however, extends far beyond merely bringing the website back online.
Unpacking The DCAD Budget: A Deeper Look at Cybersecurity Allocations
In pursuit of greater transparency and understanding regarding DCAD’s operational priorities, daltxrealestate.com submitted a formal open records request for the Dallas Central Appraisal District’s 2022-23 budget. What we received was a comprehensive, 202-page document detailing the financial allocations of the district. This extensive report offered a granular look into DCAD’s spending, including potential insights into its approach to digital security prior to the ransomware attack.
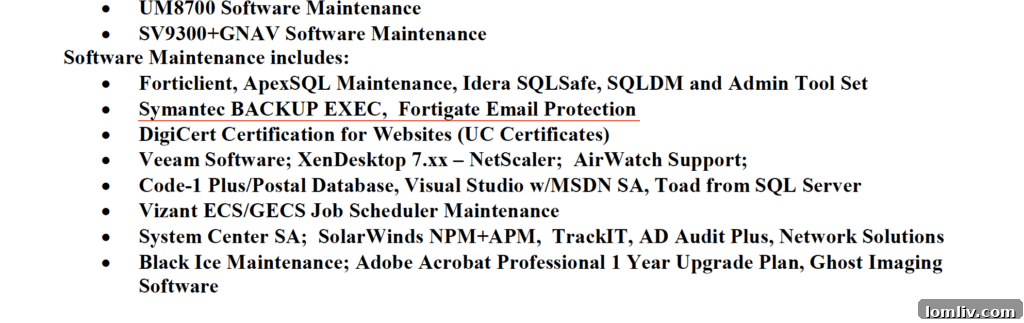
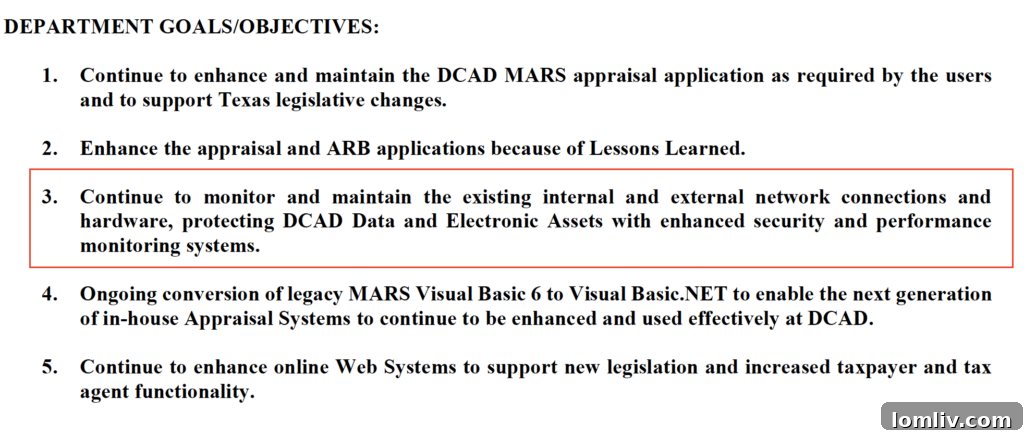
To gain expert perspective on the budget’s cybersecurity implications, we consulted Glenn Goodrich, the insightful founder and CEO of propertytax.io. Goodrich meticulously reviewed the document, highlighting specific references to “software maintenance” and an “email protection program.” While these entries indicate some level of attention to digital infrastructure, Goodrich’s analysis raised critical questions about the depth and breadth of DCAD’s cybersecurity investment.
“To have security as a priority within the budget, yet only see an email protection program somewhat buried in the line items, suggests that it might not be receiving the actual prioritization it warrants,” Goodrich observed. He further pointed out a significant omission: “I did not identify any specific allocation for a cybersecurity audit, which one would typically expect to be a distinct line item in a robust security budget. This absence implies no explicit third-party verification, which is crucial to ensure DCAD is implementing the best practices, or at the very least, the minimum required measures to achieve its security objectives.” This expert opinion underscores a potential disconnect between perceived importance and actual budgetary commitment to comprehensive digital defense.

Goodrich had previously emphasized a critical shift in DCAD’s operations. Since the onset of the COVID-19 pandemic, the district has largely transitioned to conducting the majority of its business electronically. This increased reliance on digital communication, particularly email, transforms email addresses into what cybercriminals refer to as a “honey pot.” This makes DCAD clients prime targets for sophisticated phishing campaigns, where malicious emails are meticulously disguised to appear as legitimate communications from trusted entities like Wells Fargo, Netflix, or Amazon. Such tactics highlight the evolving threat landscape and the imperative for public agencies to implement multi-layered security protocols that go beyond basic email protection.
Understanding the Threat: Dirty Links and Ransomware Tactics
In the aftermath of the breach, DCAD Chief Appraiser Ken Nolan publicly addressed the steps taken to mitigate the crisis. He disclosed that, with the full approval of the DCAD board and acting on the recommendation of a cybersecurity firm already on retainer, the district engaged a specialized third-party vendor. The vendor’s crucial role was to negotiate directly with the Royal Ransomware group, a delicate and complex process aimed at minimizing the financial impact and expediting data recovery. This decision underscores the specialized expertise required to navigate the treacherous landscape of cyber extortion.
Nolan has publicly theorized that the ransomware attack was likely initiated by an employee inadvertently clicking on a “dirty link.” Such links, often embedded in phishing emails, are meticulously crafted to appear legitimate, typically masquerading as communications from trusted vendors or internal sources. A single click can unleash malicious software, providing attackers with an entry point into an organization’s network. This scenario highlights the critical role of human error in cybersecurity breaches and the immense pressure placed on employees to identify and avoid sophisticated digital traps.
While the specifics were not explicitly detailed in the budget document, which was adopted prior to the hack, DCAD officials have confirmed significant enhancements to their cybersecurity infrastructure. The district has since brought on board a third cybersecurity company, tasked with continuous monitoring and safeguarding the entire system against future threats. Furthermore, employees are now mandated to use a robust two-step authentication process to access the system, significantly bolstering login security. A new, unique code is also implemented daily, adding another layer of defense against unauthorized access. These measures represent a proactive effort to fortify DCAD’s digital defenses and protect sensitive taxpayer data.
We also engaged with Dallas County Tax Assessor-Collector John Ames, an ex-officio board member of DCAD whose name is featured on the official budget document. When questioned about the district’s cybersecurity posture, Ames stated he was unable to comment on the specific security measures that were in place prior to the hack or detail the full scope of actions being taken to prevent future occurrences. This position, while perhaps legally cautious, contributes to the overall narrative of limited public disclosure surrounding the incident.
However, Ames did shed light on the tangible impact of the hack on his office’s operations. He explained that his team is proceeding with extreme caution in processing tax bills, recognizing the delicate nature of the situation and the importance of accuracy. A significant shift has occurred within his department: much of the business that was previously handled efficiently via email is now being conducted over the phone. “We were effectively unable to conduct normal business with DCAD for approximately two and a half months,” Ames recounted, emphasizing the profound and prolonged disruption. “We took the situation very seriously, understanding the widespread implications for taxpayers.” This operational pivot highlights the cascading effects of a major cyberattack on interconnected public services.
Tax Deadlines and Unforeseen Obstacles: No Reprieve for Property Owners
Despite the widespread disruption caused by the DCAD hack, the official property tax payment deadline remained firmly set for January 31. According to all available information, no grace period was extended to those who might have missed the deadline specifically because of the cybersecurity incident. This strict adherence to the deadline, even in exceptional circumstances, underscored the rigid structure of tax collection. However, Ames clarified to daltxrealestate.com that taxpayers who overpaid their property taxes due to the confusion or delayed information would indeed be issued refunds or receive corrective statements. This provision offered a measure of relief for those adversely affected by the data unavailability.

Adding another layer of complexity to an already challenging tax season, North Texas was battered by a severe winter storm, famously dubbed “Thundersleet Icemaggedon,” in the week leading up to the January 31 deadline. This unprecedented weather event forced the closure of numerous city and county offices, including post offices, for up to three consecutive days. The combination of the DCAD hack and the extreme weather created a perfect storm of logistical hurdles for property owners attempting to meet their tax obligations.
Emails dispatched to Ames’s office during the week of January 30, even amidst the severe inclement weather, generated automated replies that explicitly reiterated the firm stance on penalties. The message stated: “We are unable to waive penalty and interest that accrues if the payment is not received by January 31, but we are able to refund money back if the adjustment made on your account results in a lesser tax amount.” The automated response also acknowledged DCAD’s ongoing technology issues and advised contacting them by phone for specific inquiries: “Questions regarding ownership, address corrections, values, or exemptions on a property should be directed to your Appraisal District. Please be advised that the Dallas Central Appraisal District (DCAD) is currently experiencing technology issues that affect their website and emails. If you need to contact DCAD, please call their office at (214) 631-0910.” This provided a clear, if inflexible, directive to concerned taxpayers.
Ames further elaborated on the long-standing tax collection protocol. He reminded the public that property tax statements are typically issued in October and are, in fact, “due upon receipt.” This means homeowners had a substantial window of several months to process their payments well in advance of the January 31 drop-dead deadline. Acknowledging the exceptional circumstances of the recent storm and post office closures, Ames did offer a slight concession: his office would accept payments postmarked through February 3. This small extension provided a pragmatic solution to alleviate some of the immediate pressure caused by the weather, but the underlying message regarding the primary deadline remained firm. The entire episode serves as a powerful case study in how unforeseen events, both digital and natural, can profoundly impact critical civic processes and demand robust, adaptable response strategies from public service entities.
